What We Offer
Cybercriminals are coming for businesses like yours
Enterprise-grade protection, made affordable and hands-on for small and medium businesses.
Complete solution
We handpick the best solutions and make world class security affordable and available, so you do not have to decide what to buy or where to look.
Cost-effective for SMEs
We have negotiated the best prices on the market. Avoid the cost of an in-house security department, with no hidden fees.
Experienced experts
Not just automated tools. A team of experts continuously reviews, analyzes and secures your business as your personal security advisor.
Vulnerability scanning
Automatic and manual scanning of your systems to identify risks before they are exploited.
Breaches caught early
The longer a threat goes undetected, the more damage it does. We monitor continuously so threats surface fast.
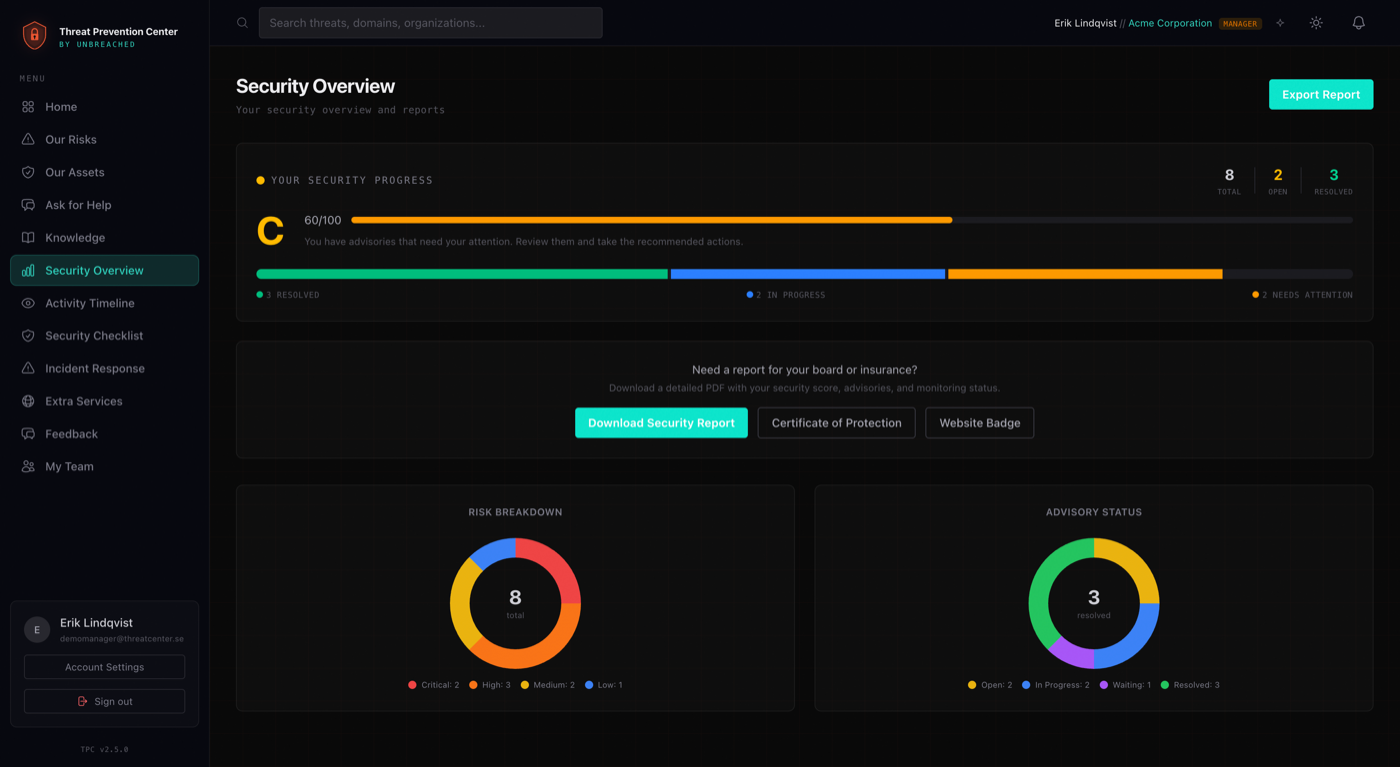
Monthly follow-up
Structured reviews with concrete recommendations and clear metrics.
Our Service
Detailed description of our threat detection capabilities
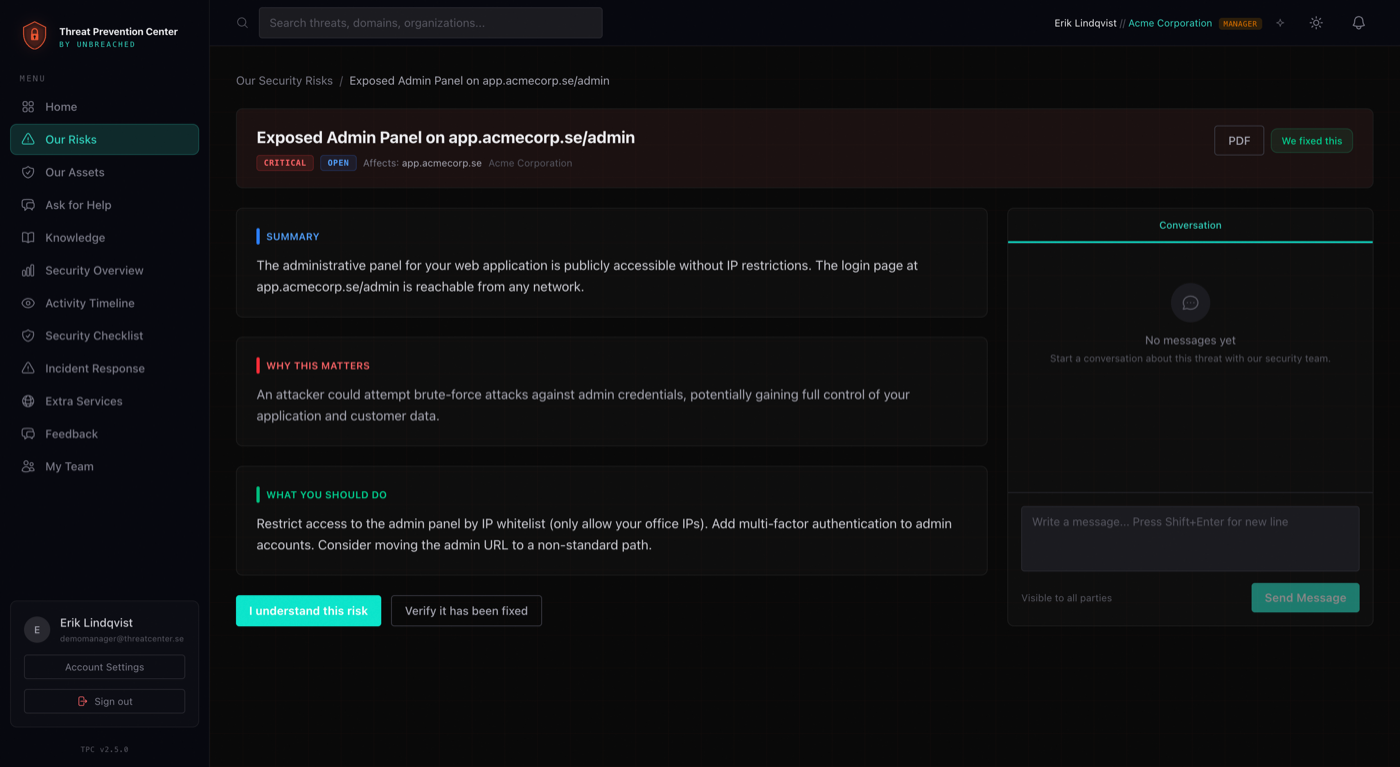
Threat Prevention Center
Each detected vulnerability is manually reviewed and categorized by our experts in the Threat Prevention Center. Instead of overwhelming you with raw technical data, we provide actionable insights detailing the consequences of each vulnerability and offering clear, prioritized solutions. This comprehensive approach ensures you have the necessary steps to mitigate risks and enhance your security posture effectively.
Threat Intelligence / Darkweb monitoring
Our comprehensive monitoring service actively scans the dark web and Telegram channels for leaked credentials, passwords, stealer logs, and other sensitive data. We identify potential threats and verify all credentials against a list of resources to ensure their validity. Verified findings are promptly reported to you via your personal Threat Prevention Center, offering a secure overview of your digital security posture. Protect your organization from data breaches with our proactive monitoring and validation process.
Threat Intelligence / Data leak monitoring
Our data leak monitoring service focuses on analyzing public data leaks for leaked credentials, passwords, and other sensitive data. We manually verify all discovered credentials against a predefined list of client resources to ensure their accuracy and relevance. The verified data is delivered to you through your personal Threat Prevention Center, providing a secure and streamlined way to stay informed about potential breaches.
Network Based Vulnerability Scanning
Our network-based vulnerability scanning uses state-of-the-art detection techniques to identify potential risks across your online services. This approach uncovers weaknesses in all connected devices, services, and protocols, providing a comprehensive view of your network's security posture. Through continuous scanning and in-depth analysis, we help you stay ahead of threats and cybercriminals, delivering ongoing insights and actionable steps to mitigate vulnerabilities before they can be exploited.
Web Application Vulnerability Monitoring
Our web application vulnerability monitoring leverages advanced payload-based scanning to uncover both known and unknown vulnerabilities. This technique is especially effective for custom-built web applications, ensuring comprehensive protection beyond standard scans. Using Surface Monitoring and Web Application Testing methods, we continuously assess your applications for security weaknesses.
Partners
Handpicked. World-leading. Proven.
We have carefully selected partners that offer world-leading security services. Combined with our expertise and hands-on approach, they form the foundation of Threat Prevention Center.
Our tools & platforms
Attack surface monitoring and automated web vulnerability scanning used by security teams worldwide.
External attack surface management and continuous vulnerability assessment across your entire infrastructure.
Nord Security's threat exposure management platform. Monitors the dark web and detects leaked credentials before they can be exploited.
The world's largest breach database. Continuously monitors for leaked credentials and exposed data tied to your organisation.
Dedicated WordPress security scanner that detects vulnerabilities, malware, and misconfigurations specific to WP environments.
Deeper security services
For customers who need penetration testing, a managed SOC, or support with ISO 27001 and NIS2 compliance, we work with Syndis. One of the most respected security firms in the Nordics.
Services offered
Penetration Testing
Professional red team operations that expose real attack paths before attackers do.
Level 3 Security Operations Center
Advanced threat detection and response with experienced analysts around the clock.
Code Review
Security experts analyse your application source code and fix vulnerabilities at the root.
ISO 27001 Certification
End-to-end support through implementation and audit to achieve certification.
Security Audit
A comprehensive assessment of your security posture, processes, and technical controls.
DPO as a Service
Dedicated Data Protection Officer for your GDPR obligations without the full-time hire.
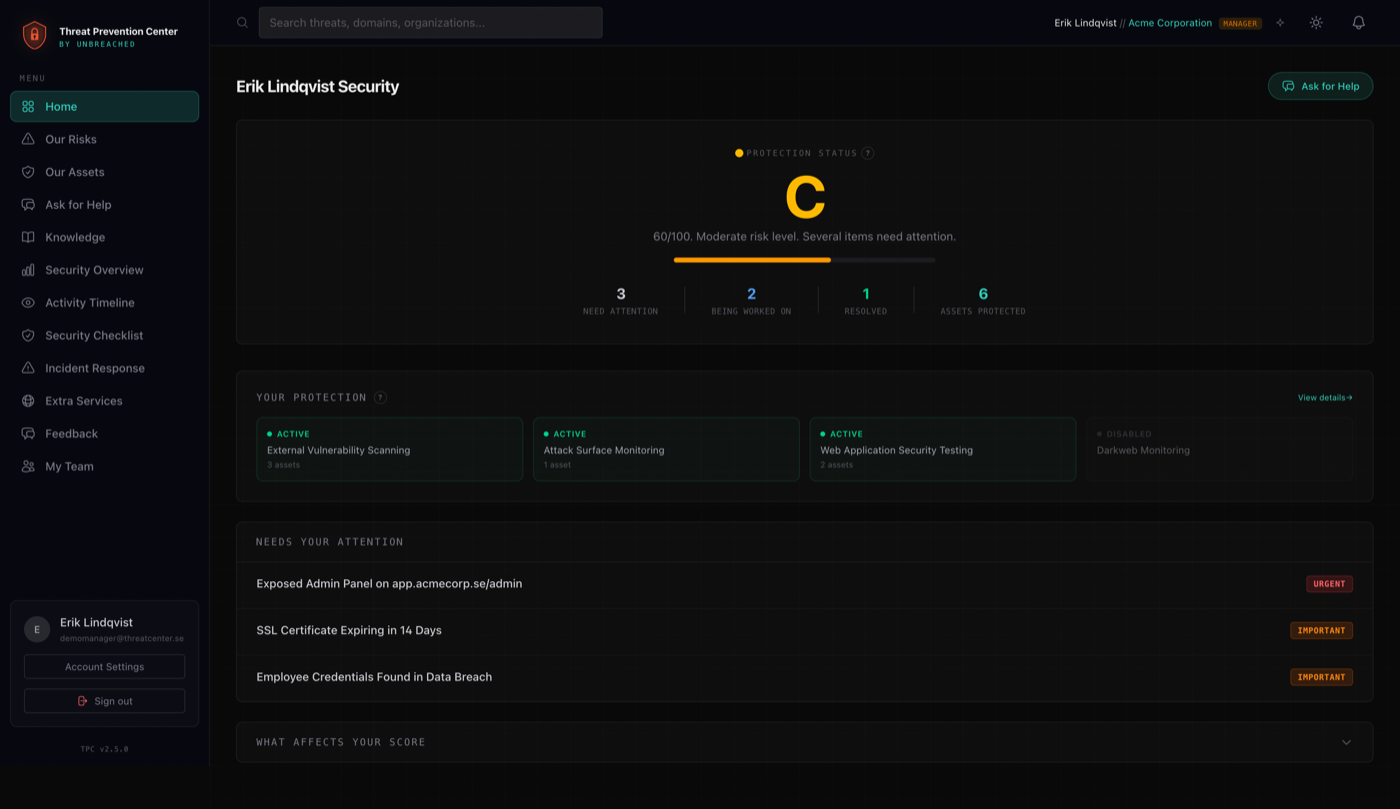
The Platform
Your security, in one place
A clear overview of your entire security posture. No raw data dumps, just what you need to know and act on.
Customers
Trusted by partners and customers
Our partnership with TPC strengthens how organizations, especially in the SME market, approach security. By combining Detectify's automated vulnerability scanning with TPC's hands-on expertise, we enable faster, smarter threat prevention.
We never had a clear picture of our actual exposure. TPC changed that. Now we always know exactly where we stand.
With TPC as a partner, we've been able to grow our team while deepening our security expertise. The personal contact has made the expansion feel completely natural and for our customers, the value is already clear, with potential attacks prevented and greater confidence in their security.
TPC stands for Threat Prevention Center. In short: we are your IT security department, without you needing to hire a single person.
Most customers are up and running within 5–10 business days. It depends a little on how complex your environment is.
No. We integrate with what you already have. We adapt to you, not the other way around.
You will be notified immediately with a concrete recommendation. On Pro and Enterprise, we handle the incident for you.
ISO 27001, NIS2, GDPR and the Swedish Security Protection Act. We provide documentation for audits and certifications.
Yes. We always start with a free risk analysis. No lock-in, no nonsense.
Contact
Let's talk.
Book a free risk analysis. No commitments, we show you where you stand today.